Key facts
- Organisation
- Vietnamese BPO Organisation — a regional business process outsourcing firm
- Threat
- Insider threat — systematic, unauthorised deletion of security monitoring components
- Initial access
- Administrative credentials belonging to current employees
- Impact
- Material reduction in threat detection, automated incident response, and operational monitoring capability
- Core issue
- No change management controls or approval requirements governing deletion of security monitoring configurations
What this case shows
- Employees with legitimate administrative access can cause irreversible operational damage without introducing any external tool, exploit, or malware.
- Security monitoring infrastructure — detection rules, watchlists, automation workflows — requires the same backup and version-control discipline applied to any other critical system. Without it, the monitoring itself becomes a target.
- The deliberate destruction of forensic evidence can be an indicator of the threat; the absence of artefacts can be a finding, not a gap.
Learn how Blackpanda’s response assurance subscriptions and compromise assessment services, when paired together, can help your organisation contain insider threats before they cause irreversible damage.
SummaryA Vietnamese Business Process Outsourcing (BPO) firm engaged Blackpanda after noticing degradation of their security monitoring environment. Analysis of audit logs found removal of detection watchlists, automation rules, operational dashboards and response workflows — not by an external attacker, but by two of its own employees.
Blackpanda found the deletions, spanning multiple days in mid-2025, attributed to two user accounts with administrative access to the security monitoring environment. One employee also deleted a web browser from their company device, destroying browser history artefacts and forensic visibility into their online activity during the relevant period.
Endpoint analysis showed both employees had high-volume activity on professional networking platforms in the weeks surrounding the deletions. One employee also accessed a personal cloud storage service, with no approved business use, from a company device on a date proximate to the deletions. While no direct evidence of data exfiltration was recovered, browser deletion and restricted log retention meant that certain activities during the relevant period could not be fully reconstructed.
Blackpanda confirmed no external malware, unauthorised remote access, or illegitimate API usage was involved. The damage was done entirely through legitimate administrative credentials — by people who had every right to be in the system.
CHALLENGE
The organisation is a Vietnamese Business Process Outsourcing (BPO) firm serving clients across the region. Central to its service delivery was a cloud-native security information and event management (SIEM) and orchestration platform — specifically Microsoft Sentinel — through which the firm’s security operations team monitored threats, managed incidents, and maintained visibility across client environments. The platform was not peripheral infrastructure, but the operational backbone through which analysts detected malicious activity, routed alerts, automated responses, and reported security posture to clients.
Within Microsoft Sentinel, the team maintained a layered architecture of monitoring components:
- Watchlists — curated reference datasets used to correlate alerts against known-bad indicators like malicious domains, flagged IP ranges, and tracked accounts — fed the detection logic.
- Automation rules governed how alerts were triaged, assigned, and escalated without analyst intervention.
- Workbooks provided the dashboards through which security posture was tracked and communicated.
- Workflow integrations routed incident notifications and reporting to internal teams and, critically, to clients.
Each component was distinct; the loss of any one of them degraded a specific capability.
The organisation noticed something was wrong when its monitoring environment began to degrade without explanation: watchlists missing; automation workflows absent; dashboards disappeared. No approved change records were present to account for any of it. The immediate operational impact was significant — watchlist-driven detections stopped working, automated alert handling ceased, and the visibility tools through which analysts and clients tracked security posture were gone.
The BPO firm requested an independent forensic investigation to determine who was responsible, whether the deletions were intentional, whether any data had been accessed or taken in addition to what had been destroyed, and what risk the incident posed to the clients.
SOLUTION
1. Establishing a Deletion Timeline from Audit Logs
Blackpanda obtained audit log data from a number of sources. Logs from the organisation’s security, identity, and monitoring systems were analysed and correlated, enabling the reconstruction of a coherent timeline of deletion events linked to specific user accounts.
One significant constraint shaped the investigation from the outset: the organisation’s log retention configuration preserved events only from Q4 2025 onward. Any activity before that time was beyond recovery.
Within the available window, deletion events spanning multiple days were identified — watchlists removed, watchlist items deleted in batches, automation rules deleted, workbooks deleted, and logic automation workflows removed in large batches. The volume, repetition, and timing of these events were inconsistent with any normal operational activity, and none were supported by approved change records at the time of review.
2. Attributing the Deletions to Two User Accounts
Both user accounts flagged by the investigation were current employees holding administrative privileges on the organisation’s security environment. The access level was appropriate to their roles as security analysts, but powerful enough to delete the detection infrastructure the organisation depended upon.
Audit log entries attributed the majority of security resource deletions to one account, and cloud storage file deletions — spanning internal security operations templates and client reporting materials — to both accounts. In several instances, Blackpanda was able to find the same deletion event appearing more than once in the audit logs, a technical artefact of rapid-succession, high-volume deletion activity rather than a logging error.
The accounts showed no indicators of compromise: no anomalous sign-in locations, no unrecognised devices, no unauthorised API calls. The credentials belonged to the employees, concluding the actions were theirs.
3. Endpoint Forensics on Two Company Devices
Blackpanda conducted forensic analysis on the two company-issued devices assigned to the investigated accounts. The analysis covered program execution history, Windows event logs, installed applications, browser artefacts, and cloud storage activity.
On one device, forensic artefacts showed that the employee deleted a web browser on a specific date and time, several days after the peak of the security environment deletion activity. The browser’s removal was not routine, and eliminated the associated forensic artefacts: browsing history, cached credentials, web-based cloud platform access records, and any evidence of authentication to third-party services during the period. As the browser and its associated data were gone, no historical browsing activity could be recovered from that application.
Neither device showed evidence of malicious software execution, persistence mechanisms such as scheduled tasks or registry autoruns, or unauthorised remote access activity. No known malicious binaries or scripts were identified. The investigation found nothing to suggest account compromise or external control.
4. Behavioural Context: Job Searching and Cloud Storage Access
Browser history analysis identified sustained and high-volume professional networking activity on both devices in the weeks surrounding the deletions. Both employees were actively browsing job listings, searching for roles in cybersecurity and IT, and updating professional profiles. This activity occurred before, during, and after the period in which the deletion events were recorded.
Job-seeking is not inherently a security event. Its relevance here lies in the temporal proximity to confirmed unauthorised actions and its consistency with a pattern of disengagement preceding departure.
One employee also accessed a personal cloud storage service — not approved for any business use at the organisation — from their company device. Due to log retention constraints, Blackpanda was unable to determine whether files were transferred during that session. Earlier accesses to the same service appeared consistent with downloading publicly available technical material and did not indicate organisational data was involved. This specific personal cloud storage access remains unresolved.
5. Scoping the Damage: What Could and Could Not Be Confirmed
Blackpanda did not identify evidence of data exfiltration from the available forensic sources. No suspicious download volumes, bulk export events, or anomalous outbound data transfers were observed from either account or device. No illegitimate API usage or abnormal authentication patterns were identified.
However, two evidentiary limitations constrained the investigation’s completeness: the restricted log retention window meant that any previous activity was irrecoverable, and the deliberate deletion of a browser eliminated the most granular record of web-based activity during the relevant period.
Exfiltration cannot be conclusively ruled out, and the investigation documented this clearly for the organisation’s HR and legal teams.
RESULTS
1. Unauthorised Deletions Confirmed and Attributed
Blackpanda confirmed that deletion activities across the organisation’s security monitoring environment and cloud storage platform were unauthorised and attributable to two specific administrative user accounts. The actions were inconsistent with business-as-usual operations and unsupported by approved change records. A complete list of identified deletion events — including timestamps, affected resources, and associated accounts — was provided to the organisation as part of the investigation update.
2. Material Operational Impact Established
Blackpanda established that the combined deletions materially reduced the organisation’s security monitoring capability across three dimensions. Watchlist-driven detections — used to identify malicious domains, suspicious network indicators, and flagged accounts — were disrupted. Automated incident handling, including triage, notification routing, and response actions, ceased to function. The dashboards through which analysts and clients tracked security posture and incident trends were removed. The BPO firm’s monitoring effectiveness was materially impaired at a time when its clients’ environments remained exposed to external threats.
3. No External Threat Actor Involved
Endpoint forensic analysis, log review, and authentication analysis found no evidence of external compromise. No malicious software was executed on either device, no unauthorised remote access was observed, and no illegitimate API activity was identified. The damage resulted entirely from current employees operating within their existing access privileges — credentials they legitimately held, used for purposes entirely outside the scope of their employment.
4. Deliberate Evidence Destruction Identified as an Independent Finding
The deletion of a web browser from a company device — occurring days after the security monitoring environment deletions and immediately after a period of confirmed unauthorised activity — was assessed as a material finding in its own right. The action eliminated browser history artefacts that would otherwise have provided direct visibility into online activity during the relevant period. Whether the browser deletion reflected an intent to conceal is a question for HR and legal processes; what the forensic record established is that specific evidence was removed, and that its removal constrained the investigation’s completeness. That constraint is itself documented and will be relevant to any subsequent proceedings.
5. Recommendations for Immediate Action and Systemic Remediation
Blackpanda provided the organisation with a structured set of recommendations.
Immediate actions:
- Review and restrict administrative privileges across security, identity, and monitoring systems, and related platforms.
- Disable the identified accounts pending HR and legal review.
- Implement formal change management and approval processes for all resource deletions and modifications in the security monitoring environment.
Structural remediation:
- Enable resource locks on high-value security components.
- Implement version-controlled, regular backups of watchlists, automation rules, workbooks, and workflows.
- Extend log retention periods across the security stack to improve forensic visibility in future investigations.
- Enforce conditional access policies to prevent use of non-approved cloud storage services from company devices.
The investigation surfaced a systemic gap that is neither unusual nor specific to this organisation. Security monitoring infrastructure is routinely left unprotected by the same controls applied to everything else. Watchlists and automation rules can be deleted by any administrative user, at any time, without approval or escalation. An environment where the detection machinery is itself unprotected is one where an insider with the right credentials and the wrong intentions faces no practical obstacle.
FAQ
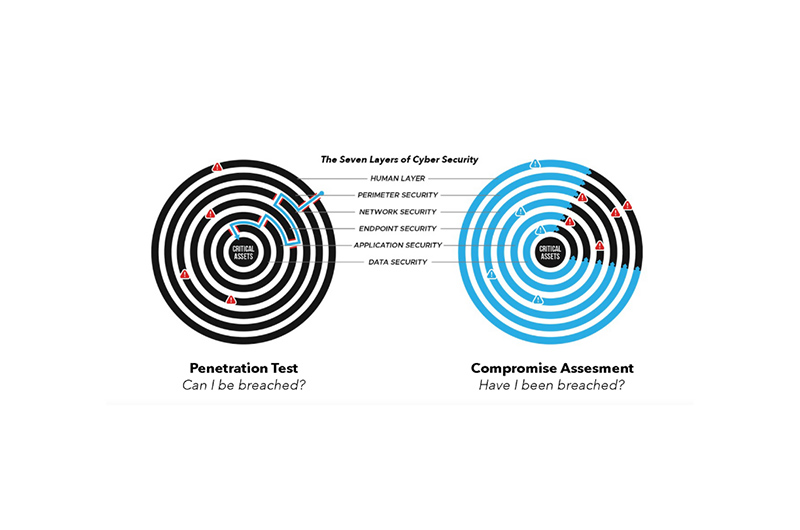
1. What is an insider threat, and how does it differ from an external attack?
An insider threat is any security risk originating from within an organisation — a current employee, a former employee, a contractor, or any party with authorised access to internal systems. Where an external attacker must first overcome the organisation’s defences to gain a foothold, an insider already has one. This distinction makes insider threats particularly difficult to catch using conventional security tools as the actions can be indistinguishable, at first glance, from legitimate work.
In this case, the two employees used their own administrative credentials through the standard management interface. There was no exploit, no malware, no intrusion. The threat was invisible until the damage was done.
CISA’s Insider Threat Mitigation resources provide a useful framework for organisations building detection and response capabilities.
2. How did employees with regular job roles have access to cause this much damage?
Both employees were security operations analysts, roles for which administrative access to their security monitoring environment is operationally appropriate. Analysts need to create and modify watchlists, build automation rules, and configure workbooks as part of their daily work.
The problem is not that administrative access was granted; it is that no controls governed what administrators could delete. Most organisations implement access controls that determine who can do what, but fewer implement approval workflows specifically for destructive actions like deletion of high-value resources. In this environment, an authenticated administrator could remove detection infrastructure at will, without triggering any approval process, escalation alert, or audit flag.
3. How did the investigation establish that the deletions were unauthorised?
The investigation assessed the deletion activities against two criteria: consistency with business-as-usual operations, and support from approved change records. Neither was satisfied.
The volume of deletions — spanning multiple categories of detection resources across multiple days — was inconsistent with routine maintenance. No change record existed for any deleted resource. The pattern of repetition, the targeting of detection infrastructure specifically, and the deletion of a web browser in the days following activity within the security monitoring environment were assessed collectively as indicators of intentional action.
The investigation stopped short of establishing intent as a legal matter — that responsibility lies with HR and legal to process — but the forensic picture was unambiguous.
4. Could an organisation like this realistically not have noticed sooner?
Yes, and it is more common than it appears. Security monitoring degradation is often gradual and easy to misattribute: a missing watchlist might initially read as a configuration issue, a deleted automation rule as a workflow error, an absent dashboard as a platform glitch. In environments where the monitoring infrastructure was built incrementally over time — added rule by rule, watchlist by watchlist — the removal of individual components may not trigger an immediate visible alarm.
The absence of an audit alert on deletion events is part of the same systemic gap. Without resource locks or deletion-triggered escalations, the monitoring system had no mechanism to flag that it was being dismantled.
5. Why couldn’t the investigation confirm whether data was exfiltrated?
Two constraints. First, the organisation’s log retention configuration preserved events only from Q4 2025 onward, so any access or transfer before that date was irrecoverable. Second, the deliberate deletion of a web browser from one company device destroyed the browser history, cached credentials, and web-based platform access records that would have provided the clearest view of online activity during the relevant period. Network-level firewall logs, which would give the most direct evidence of outbound data transfer, were not available. These gaps are documented in the investigation record and are directly relevant to any subsequent HR, legal, or insurance proceedings. NIST’s Guide to Integrating Forensic Techniques into Incident Response (SP 800-86) addresses how log retention affects forensic completeness.
6. What controls would have prevented or limited this incident?
Several controls, applied in combination, would have materially reduced the damage. Resource locks on high-value security monitoring components prevent deletion without an explicit lock-removal step, adding friction and an audit trail to any destructive action. Regular export-based backups of watchlists, automation rules, and workbooks ensure that deleted resources can be restored quickly, limiting operational disruption. Approval workflows for security monitoring resource deletions — for example, requiring a second authorised reviewer before any deletion is processed — remove the ability for a single employee to act unilaterally. Deletion-triggered alerting creates an immediate escalation path when a critical resource is removed. Extended log retention reduces the forensic blind spot created when incident windows predate the available log history.
None of these controls is technically complex; the gap in this case was that none of them was in place.
WHAT THIS MEANS FOR YOUR ORGANISATION
Every security team operates on the assumption that it is watching outward. The perimeter is logged. External connections are monitored. Detection rules are tuned to catch what comes in from outside.
Less often examined is whether the monitoring infrastructure itself — the watchlists, the automation rules, the dashboards, the workflows — is subject to the same governance, backup, and access controls applied to everything else. This case makes the failure to do so concrete.
A company lost its threat detection capability not because an external attacker defeated its defences, but because internal staff with legitimate access chose to delete them. There was no vulnerability to patch, no attack vector to close, no external party to block. The access was legitimate, and the destruction was the point. And because the environment had no resource locks, no deletion-approval process, and no backup mechanism for its own detection configurations, there was nothing to stop it.
The irony here is worth consideration: the organisation’s business was monitoring security for itself and for its clients, and the infrastructure that was destroyed was the infrastructure on which clients depended. An insider who corrupts or dismantles a managed security provider’s monitoring environment does not just affect the provider; they affect every client whose protection passes through it. For organisations that carry this kind of responsibility, insider threat governance is not a secondary consideration. Blackpanda’s response assurance subscriptions provide organisations with an independent incident response capability that sits outside the internal environment — ensuring that when something goes wrong inside, the escalation path is not also inside.
ABOUT BLACKPANDA
Blackpanda is a Lloyd’s of London–accredited insurance coverholder and Asia’s leading local cyber incident response firm, delivering end-to-end digital emergency support across the region. We are pioneering the A2I (Assurance-to-Insurance) model in cybersecurity — uniting preparation, response, and insurance into a seamless pathway that minimises financial and operational impact from cyber attack. Through expert consulting services, response assurance subscriptions, and innovative cyber insurance, we help organisations get ready, respond, and recover from cyber attacks — all delivered by local specialists working in concert.
Our mission is clear: to bring complete cyber peace of mind to every organisation in Asia, from the first moment of breach through full recovery and beyond.